Patrol Monitoring – What it is?
How it works?
The BCS patrol monitoring system combines the best of durable hardware and intelligent software to ensure absolute site security across industries. By digitizing the entire process, the system transforms physical movements or touchpoints into actionable data. Managers can monitor progress, eliminate reporting gaps, and maintain 100% operational transparency from start to finish.
Patrol Monitoring Illustration

It is time for guard to begin his patrol

The guard reads a checkpoint along his patrol route
This equipment is vandalized!

The next image using “incident wallet”
The guard does his patrol route
The guard return to his room

He downloads the data in the wand to his computer
The reports are printed and the manager reads the report
- Would You Like to Have a
Free Trial For 60 Days?
The problem
Whether it’s a hospital wing, a piece of factory equipment, or a million-dollar painting, security guards are entrusted with the vital task of protecting what they are responsible for. However, unlike office workers, security guards may work at odd hours and with little to no supervision. Many work alone at night in warehouses, office buildings, or institutions. They may be responsible for fulfilling a range of regular patrol duties, such as checking the entrance to a building every hour.
Without any supervision, a security guard might be tempted to stray off-task. They might check their phones and lose track of time or even go off-site.

The solution

Hardware
Checkpoints :These are button-sized “tags” containing unique identification numbers which can be read by a portable electronic reader. They can be fixed to the wall at each point that your employee needs to inspect.
Different kinds of tags can be used, such as barcodes, RfID, Touch Memory, QR Codes, NFC, and GPS locations for virtual checkpoints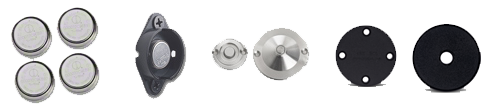
Portable Readers or Wands: Portable electronic readers are used to read the Ids of the tags. During a patrol, the readers are used to read (“scan”) the tags at checkpoints along the patrol route. When a reader read the tags, the reader records the tag’s unique ID as well as the date and time.
Mobile phones with a specialized app are also used in place of dedicated tag readers.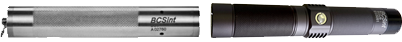
Setting up the monitoring system
Checkpoints are first affixed to important points of inspection along the security guard’s patrol route.
Next, the Security Guard is given:
- A Reader to scan the Checkpoints
- A Guard Button to identify himself (optional)
- An Incident Wallet to record incidents (optional)

How does it work?
As the security guard does his patrol route, he uses the Reader to scan checkpoints that he passes along the way.
The reader records the checkpoint id and the current date and time. He can also use the reader to record any incidents that occur.
At the end of the patrol, the guard places the reader in the downloader and the information is transferred to a computer with the Patrol Monitoring Software for processing.
If the guard has a Guard tag, he uses the reader to scan it to link him with the route he is about to start.
The software can then be used to produce reports to verify that the patrols were done or to report on any missed checkpoints or incidents.
Note: If a mobile phone with an app is used as the reader:
- downloaders are not needed since the mobile phone will send the data directly to the software over the internet
- Guard tags are not needed since they must log in to the Mobile App with their user name
- Incident tags are not needed since incidents can be defined and sent via the App
Our software can be customized based on your needs:
- Predefined times for patrols
- Predefined intervals between checkpoints
- Random or sequential checkpoint reading
- Real time checkpoints reading